Event logging is a crucial part of a strong cybersecurity strategy. It helps businesses spot security breaches and respond quickly. Businesses today face a rising wave of cyberattacks, from ransomware to phishing. A strong cybersecurity strategy is essential to stay ahead of these threats. One crucial component of this strategy is event logging . Not every business owner knows the importance of event logging. Think of it as a digital detective that helps spot security breaches and enables quick response. As your IT provider, we’ll help you understand and implement best practices to protect your network.
What is Event Logging?
Event logging is the act of tracking all events that happen within your IT systems. “Event” can be many different things, such as:
- Login attempts
- File access
- Software installs
- Network traffic
- Denial of access
- System changes
- And many others
Event logging means to track all these and add a time stamp. This provides a robust picture of what is going on in your IT ecosystem. It’s through that ongoing picture that you can detect and respond to threats promptly. Why is it critical to track and log all these events?
· Detect suspicious activity by monitoring user behavior and system events.
· Respond quickly to incidents by providing a clear record of what happened in a breach.
· Meet regulations that require businesses to maintain accurate records of system activities.
Best Practices to Use Event Logging Effectively
Event logging is most effective when you follow best practices. Here are some standard guidelines to follow. These are helpful if you’re just starting out as well as for those improving existing event-logging processes.
Log What Matters Most
Let’s be honest: You don’t need to track every digital footstep. Logging every single action on your network can create a mountain of data that’s hard to sift through. Instead, focus on the events that truly matter. These are those that can reveal security breaches and compliance risks. The most important things to log are:
· Logins and Logouts: Keep tabs on who’s accessing your systems and when. This includes failed attempts, password changes, and new user accounts.
· Accessing Sensitive Data: Track who’s peeking at your most valuable information. Logging file and database access helps spot unauthorized snooping.
· System Changes: Keep a record of any changes to your system. Including software installations, configuration tweaks, and system updates. This helps you stay on top of changes and identify potential backdoors. Event logging is much more manageable when you start with the most critical areas. This also makes it easier for small businesses.
Centralize Your Logs
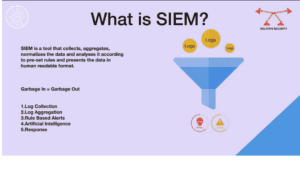
Working with logs from different devices and systems is like solving a puzzle with pieces scattered in other rooms. Centralizing logs with an SIEM brings them together in one place, including those from devices, servers, and applications. This makes it easier to:
· Spot patterns: Connect the dots between suspicious activities across different systems.
· Respond faster: Have all the evidence you need at your fingertips. This is helpful when an incident strikes.
· Get a complete picture: See your network as a whole. This makes it easier to identify vulnerabilities.
Ensure Logs Are Tamper-Proof
It’s important to protect your event logs! Attackers love to cover their tracks by deleting or altering logs. That’s why it’s vital to make your logs tamper-proof. Here are some tips:
· Encrypt your logs: Lock them down with encryption. This makes them unreadable to unauthorized eyes.
· Use WORM storage: Once a log is written, it’s locked in place, preventing changes or deletions.
· Use strong access controls: Limit who can see and change your logs to trusted personnel only. Tamper-proof logs provide an accurate record of events even if a breach occurs. They also keep the bad guys from seeing all your system activity tracking.
Establish Log Retention Policies
Keeping logs forever isn’t practical (or always necessary). But deleting them too soon can be risky, too. That’s why you need clear log retention policies. Here are some things to consider:
· Compliance requirements: Some industries have specific rules about how long to keep logs.
· Business needs: How long do you need logs to investigate incidents or for auditing?
· Storage capacity: Make sure your log retention policy doesn’t overwhelm your storage. Strike the right balance with retention. You want to ensure you have the data you need without sacrificing performance.
Check Logs Regularly
Event logging is only effective if actively used. Don’t just “set and forget” your logs—check them regularly to spot anomalies and threats early. Security software can help automate this process.
Here’s how to do it effectively:
· Set up automated alerts: Get notified immediately of critical events. Such as failed logins or unauthorized access.
· Perform periodic reviews: Dive into your logs regularly. Look for patterns that might show a threat.
· Correlate events: Use your SIEM to connect the dots between different activities. It can reveal more complex attacks.
Need Help with Event Logging Solutions?
As a trusted managed IT service provider, we’re here to support you. We can help you install these practices and ensure your business stays protected.
Reach out to us, give us a call or email to schedule a chat.